Big Sur brought about a lot of cool changes. However, there was one “improvement” that wasn’t popular with people who care about their privacy – the fact that Mac apps could bypass VPN services.
How were they able to do that, and are all VPNs affected by that issue? Find out everything you need to know in this article. We’ll also tell you whether or not Apple fixed the issue (spoiler: they did).
Page Contents
So What’s Big Sur’s Problem with VPNs?

Source: hidemyass.com
Well, it looks like the update made it possible for Mac apps to bypass VPN tunnels. Basically, apps like Siri and FaceTime could communicate directly with Apple’s servers without having to use the VPN tunnel.
Normally, if you were to use – let’s say – FaceTime with a VPN, your connection would look like this:
Your Mac ? ISP Network ? VPN Server ? Apple’s Servers
But if you did that on Big Sur, your connection would look like this:
Your Mac ? ISP Network ? Apple’s Servers
Yes, the apps would pretty much ignore the encrypted VPN tunnel. So while you were using them, a lot of your data would leak outside the VPN connection.
What does that mean, exactly?
That Apple would still be able to see and track your real IP address through its apps. Normally, it should only see the VPN’s IP. In case you didn’t want Apple’s services to know what country you’re from, you wouldn’t be able to stop them from learning that.
And that’s not all! The traffic leaks also meant that cybercriminals could spy on your Mac’s app traffic. They could abuse this vulnerability to steal sensitive information from you or redirect your connections to malicious servers and domains.
How Was That Possible?
Big Sur apparently introduced a new key in the NetworkExtension API: ContentFilterExclusionList. Many security programs use that API, and that specific key would force them to ignore Apple’s apps.
What Are the Security Implications?

Source: hsees.rs
Besides the dangerous traffic leaks and privacy breaches?
Well, there’s also the fact that the Big Sur update would force firewalls to ignore Mac apps too. That means firewalls couldn’t protect you from hackers anymore. If they would be able to find a security hole in the apps, they could easily exploit it and infect your Mac with malware.
Are All VPNs Susceptible to the Forced Leaks?
That’s not the case, luckily. Only security software that relied on the NetworkExtension API would be at risk of suffering traffic leaks. Many top providers don’t do that, so they’re safe to use.
Also, the VPN would need to have a kill switch to make sure you’re 100% protected. That way, if the VPN connection would go down, you wouldn’t be able to go online until it reconnects.
How to Find the Best Mac VPN
With so many VPNs on the market, finding a good one can be hard. Don’t worry – we’ll make it easy for you! Just click here to see a list of the best Mac VPNs.
Is This Issue Still Present in Big Sur?
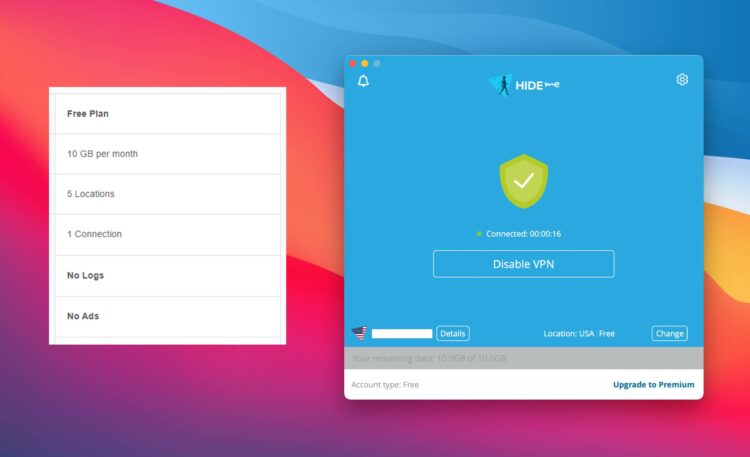
Source: techsviewer.com
Not if you use Big Sur 11.2. That version turned off the troublesome key which caused the VPN and firewall leaks. Besides that, this version also introduces a few other improvements:
- Bluetooth connections are more reliable.
- Other small vulnerabilities received a security patch.
- Other bugs and issues were fixed. For example, you should no longer see black screens on external displays whenever you use an HDMI to DVI converter with your Mac mini.
Big Sur 11.2 actually isn’t the latest release. Big Sur 11.2.1 recently came out. Updating to it isn’t necessary to fix the VPN/firewall security issue. Right now, it looks like 11.2.1 just fixes one issue with 2016 and 2017 MacBook Pro models – specifically the fact that the battery sometimes didn’t charge.
How to Update to the New Big Sur Version
Just follow these steps:
- Click the Apple menu, and pick About this Mac.
- Open the Overview tab (if it’s not already opened).
- Look for Software Update and click it.
- (Optional) If you want to learn more about the update, click More Info.
- Click Update Now to start the installation. It might take a few minutes since the update is about 3.66 GB.
Why Apple Didn’t Do This on Purpose

Many people like to speculate that Apple’s mistake was intentional. It’s an interesting conspiracy, don’t get us wrong, but it’s not grounded in reality.
First of all, Apple’s built-in VPN function still worked after the Big Sur update. It didn’t suffer any leaks. You could argue that Apple’s VPN is compromised, sure, so let’s move on to the next point.
Market dominance. Why would Apple intentionally cripple their devices when most companies that sell computers require them to have support for VPNs? It just doesn’t make sense. If Apple really were to compromise VPNs and firewalls like that, they’d lose a big share of the market overnight.
Apple’s devs slipping up and making a mistake makes more sense. They’re only human, after all. So these kinds of errors can happen. What matters is that they managed to fix them in time.
To Sum It All Up
When Apple released Big Sur, it overlooked one issue – a specific key that triggered traffic leaks in VPNs and firewalls by allowing Apple’s applications to bypass them. Fortunately, not all VPNs were affected by this problem. Also, Apple patched this vulnerability with their Big Sur 11.2 release. Be sure to update to it as soon as possible.
If you have other questions about the Big Sur privacy issue, or about using VPNs on Mac, please let us know in the comments. We’ll do our best to get back to you as fast as we can.